Article
In conversations with operations, IT and architecture leaders, one question comes up most frequently: “What makes a SOAP different from our scheduler or iPaaS — and why should we invest now?”
It’s a fair question. And the answer isn’t just focused on why you should add another automation tool. Instead, considering a Service Orchestration and Automation Platform (SOAP) means you’re ready to think about the operational model behind how work moves across your organization.
A scheduler triggers tasks, an iPaaS connects applications, but a modern SOAP coordinates end-to-end business processes across systems, teams and environments in a way that maintains reliability at enterprise scale. That difference shows up directly in operational resilience, business agility and cost control.
The 2025 Gartner® Critical Capabilities for SOAP report is the clearest framework I’ve seen for tying platform strengths to financial outcomes. Here’s how I help leaders like you use that framework to build a credible business case.
The framework: Mapping Use Cases to your P&L
The Critical Capabilities report doesn’t start with architecture diagrams or methodology. It starts with how platforms perform against five operational Use Cases, each representing a measurable part of your business. I find these especially useful because they line up almost perfectly with the major categories of cost, risk and productivity that executives care about:
- Operational resilience
- Business agility
- Cost optimization
- Risk management
- Speed to insight
Instead of thinking of them as technical buckets, think of them as the five pillars that determine whether your automation investments actually return value. A SOAP that scores well across all five transforms automation from a technical initiative into an engine for enterprise performance.
Pillar 1: IT workload automation and the ROI of unbreakable operations
The business challenge:
A pervasive pattern I see is IT teams stuck in a reactive mode. Excessive time is spent on firefighting and manual monitoring, which draws focus away from strategic process improvement. This reactive posture results in costly consequences, including missed service-level agreements (SLAs), silent failures in critical overnight processes and a constant backlog of expensive incidents.
What this Use Case measures:
Gartner considers this the foundation of SOAPs: Can the platform run critical workloads reliably across hybrid and multi-cloud environments? Think financial close, inventory syncs, regulatory reporting — with real-time awareness and automated recovery. This means it must offer dependency management that understands system context, recovery paths that prevent cascading failures and observability that lets operators diagnose and resolve issues quickly.
Where the ROI shows up:
- Reduced downtime costs: Preventing failures before they hit the business
- Lower operational overhead: Fewer hours spent monitoring or intervening
- Strategic consolidation: Eliminating multiple schedulers, licenses and skillsets
This is the first place most organizations find real cost savings, because reliability is expensive when you’re compensating for it manually.
Pillar 2: IT workflow orchestration and the value of cross-team agility
The business challenge:
Most delays don’t come from individual tasks. They come from the handoffs: the approvals that get stuck in someone’s inbox, the data that wasn’t validated, the system that didn’t trigger the next step. Teams often automate inside their own domains but leave the gaps between them unmanaged.
What this Use Case measures:
Gartner looks at how well a SOAP can coordinate entire processes, not just tasks:
- Cross-application workflows (ERP + ITSM + SaaS + custom apps)
- Conditional logic and exception handling
- Orchestration spanning on-premises and cloud environments
Where organizations see ROI:
- Shorter cycle times: End-to-end processes move without waiting on human intervention
- Higher throughput: Fewer restarts, errors or duplicate work
- Greater adaptability: Workflows that adjust as business requirements change
The payoff is simple: people get hours back. Not to mention, change doesn’t feel risky anymore.
Pillar 3: Data orchestration and the payoff of faster, smarter decisions
The business challenge:
Analytics teams can only move as fast as the data feeding them. Many organizations are still juggling multiple disjointed ETL solutions, insecure file transfers or inconsistent handoffs between systems. The result is predictable: delays, inconsistent data and missed windows for decision-making.
What this Use Case measures:
Gartner evaluates a SOAP’s ability to orchestrate reliable, governed data pipelines:
- Event-driven movement from systems like SAP to data warehouses like Snowflake
- Managed file transfers with dependency tracking
- Data validation, reconciliation and exception handling
- Automated triggers to BI, AI or other downstream applications
Where organizations see ROI:
- Faster time-to-insight: Data arrives validated and on time
- Improved compliance: Centralized audit trails remove the risks of custom scripts with no single source of truth
- Eliminated bottlenecks: Analytics teams spend less time waiting and more time analyzing
This is where organizations often unlock value they didn’t realize they were losing.
Pillar 4: Citizen automation and the advantage of empowered teams
The business challenge:
IT teams become bottlenecks when every routine request — from report generation to onboarding steps — has to be manually actioned. The backlog grows and the business slows.
Yet handing automation directly to business users without governance isn’t an option.
What this Use Case measures:
Gartner evaluates this capability by looking at how well a platform can distribute automation safely without losing control. It’s essentially a test of whether your Operations team can create guardrails that let business users trigger approved workflows on demand without introducing risk. A strong score here reflects a platform that supports low-code execution, reusable templates and full auditability, so non-technical users can initiate routine actions while IT retains oversight. This Use Case ultimately measures how effectively a SOAP can push automation closer to the edge of the business without allowing fragmentation or shadow IT to creep back in.
Where organizations see ROI:
- Faster turnaround: Teams get what they need without waiting days or weeks
- Reduced IT ticket volume: Freeing technical staff to focus on higher-value work
- Fewer errors: Standardized workflows eliminate risky and error-prone manual steps
When done right, citizen automation is not “shadow IT.” It’s a controlled extension of enterprise automation.
Pillar 5: DevOps automation and the competitive edge of continuous delivery
The business challenge:
Software teams often automate their CI/CD pipelines but leave the surrounding processes — environment provisioning, test data setup, dependency coordination — untouched. Those manual steps are what slow releases and introduce inconsistencies.
What this Use Case measures:
For DevOps automation, Gartner focuses on how deeply the platform can integrate into modern delivery pipelines and how reliably it can coordinate the steps surrounding deployment. It’s about assessing whether automation can move at the same pace as engineering, from provisioning and testing to promotion and release. High-performing platforms demonstrate support for automation-as-code practices, event-based triggers and consistent orchestration across environments. Use these parameters to gauge a provider’s ability to remove bottlenecks from the software lifecycle so teams can deliver changes quickly without compromising reliability or governance.
Where organizations see ROI:
- Shorter release cycles: Faster, safer path from commit to production
- Higher developer productivity: Fewer manual tasks around the deployment lifecycle
- More reliable deployments: Consistency enforced across environments
This is increasingly a strategic differentiator for teams moving toward cloud-native delivery models.
An undeniable case for a strategic investment
A scheduler reduces manual effort, whereas a SOAP reduces friction across your entire operating model. When a single platform delivers across all five Gartner Use Cases, you’re not just buying automation capabilities — you’re buying:
- Fewer outages
- Faster decisions
- Higher team velocity
- Lower integration costs
- Stronger risk posture
- A future-proof automation foundation
This is the business case every CFO wants: clear outcomes tied to operational, financial and strategic value. The next time you evaluate platforms, don’t ask, “What does it automate?” Ask, “Where does it impact my P&L?”
That’s the difference between a tool and a transformation partner.
Evaluate SOAP vendors with our scorecard, and download the full Gartner Critical Capabilities report to compare how leading platforms perform against these five essential Use Cases.
Uncategorized
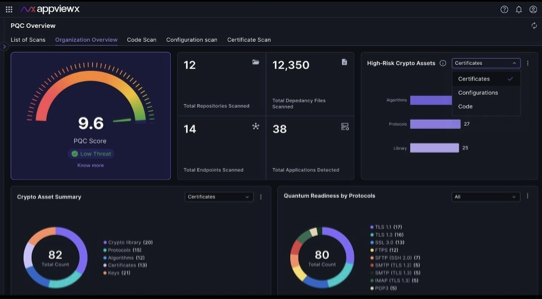
With its latest release, AppViewX delivers new CLM and quantum-safe innovations to help organizations strengthen security, reduce compliance gaps, and maximize time to value
NEW YORK, Dec. 03, 2025 (GLOBE NEWSWIRE) — AppViewX, the leader in automated Certificate Lifecycle Management (CLM) and Public Key Infrastructure (PKI) software, today announced significant enhancements to its AVX ONE Platform, enabling enterprises to meet the upcoming 47-day SSL/TLS certificate validity mandate with speed and confidence. The release also introduces new automation and quantum-safe capabilities that simplify compliance, improve security posture, and deliver measurable ROI.
As certificate lifespans shrink rapidly over the next few years, the result will be surging renewal volumes, which will lead to significant operational and compliance risks for organizations. The AVX ONE platform eliminates these challenges by automating certificate discovery, provisioning, renewal, and revocation, ensuring continuous compliance with crypto-agility across hybrid and multi-cloud environments.
“Our customers need a future-proof solution that transforms regulatory pressure into operational excellence,” said Paul Trulove, Chief Product Officer at AppViewX. “This release underscores our commitment to rapid time-to-value, measurable ROI, and innovation that helps enterprises succeed in the age of 47-day certificates and a post quantum computing world.”
AppViewX Product Release Highlights
Manage Short-Lived Certificates at Scale
Automate renewal cycles and enforce re-enrollment policies to meet 47-day mandates without added overhead. Gain flexible control over certificate lifespans, automatically generate new private keys for improved security and leverage enhanced reporting for continuous compliance.
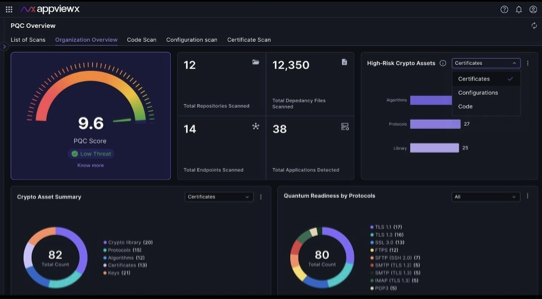
Advance Crypto-Agility and PQC Readiness
Demonstrate leadership in post-quantum preparedness with a comprehensive list of cryptographic assessments and remediation. AppViewX generates a Cryptographic Bill of Materials (CBOM) across certificates, algorithms, libraries, and applications, with clear remediation recommendations and a unified dashboard for executive reporting.
Gain Actionable AI Insights
Use natural-language search and AI-driven dashboards to get instant visibility into certificate operations with no scripts or technical queries required. AI-enabled navigation makes complex tasks effortless (such as “rotate a certificate,” “add a device group”, etc.) and saves time.
Accelerate Time-to-Value and ROI
Use predefined policy templates and out-of-the-box onboarding to dramatically reduce setup time. Enterprises can deploy in days, standardize compliance, and prove ROI faster, turning regulatory pressure into a business advantage.
Driving ROI in the Age of 47-Day Certificates
With its latest release, AppViewX ensures enterprises can:
- Improve certificate lifecycle automation with key enhancements to meet CA/B Forums new 47-day mandate
- Reduce operational costs, improve user experience and accelerate time to value.
- Demonstrate leadership in PQC readiness.
- Empower teams with AI-driven visibility and insights.
Availability
The November 2025 Product Release is available immediately from AppViewX. For details, read here.
See Innovation in Action: Gartner IAM
AppViewX will showcase its latest CLM and PQC innovations at the 2025 Gartner Identity & Access Management Summit in Dallas, December 8–10 (Booth #227). To see a demo or reserve your seat for our VIP dinner, register here.
As PQC timelines accelerate, organizations must begin foundational steps, starting with visibility and inventory, as early as next year. According to Gartner®, “No later than mid-2026, build and maintain a complete inventory of cryptographic assets to inform postquantum cryptography (PQC) migration planning.”¹
1Gartner, “Post-Quantum Cryptography: Why You Need to Be Ready by 2030” by Mark Horvath and Sarah Almond, October 27, 2025.
Gartner is a registered trademark of Gartner, Inc. and/or its affiliates in the U.S. and internationally, and is used herein with permission.
Uncategorized
Key Takeaways
- TLS certificates shrink from 398 days to 47 days by March 15, 2029, requiring 7,766 annual renewals per 1,000 certificates
- CA/Browser Forum Ballot SC-081v3 passed with 29 votes in favor, zero opposed, signaling unanimous industry alignment
- Three-phase implementation: 200 days (March 2026), 100 days (March 2027), 47 days (March 2029)
- Organizations implementing automation now gain 2-3 year advantage in operational excellence and cost efficiency
- Domain validation reuse drops to 10 days by March 2028, requiring weekly revalidation cycles
- Crypto-agility becomes essential for preparing for post-quantum cryptography transitions by 2035
The cybersecurity landscape is undergoing its most significant transformation in the history of certificate management. When the CA/Browser Forum approved Ballot SC-081v3 in April 2025, it set in motion a fundamental shift that will redefine how organizations approach digital trust. This comprehensive guide examines the 47-day certificate mandate, its timeline, industry impact, and implications for your organization’s security posture.
What Are 47-Day Certificates?
The Fundamental Change
A 47-day certificate represents the new maximum validity period for publicly trusted TLS certificates, effective March 15, 2029. This dramatic reduction fundamentally alters the operational dynamics of certificate lifecycle management. Where organizations currently renew certificates roughly once per year, the 47-day model requires renewal every six to seven weeks, a ninefold increase in renewal frequency.
The change extends beyond simple validity reduction. Domain control validation, currently reusable for up to 398 days, will shrink to just 10 days by March 2028. This means organizations must prove domain ownership roughly every week and a half, adding another layer of operational complexity to certificate lifecycle management.
Historical Context of Certificate Validity Periods
Understanding the 47-day mandate requires examining the evolution of certificate lifespans:
- Pre-2011: Certificates valid for 5+ years were common
- 2012-2015: Industry moved to a 3-year maximum
- 2015-2018: Reduced to 2-year maximum (825 days)
- 2018-2020: Further reduced to 1 year + renewal buffer (398 days)
- 2020-present: Current 398-day maximum
- 2026-2029: Phased reduction to 47 days
Each reduction has strengthened security while increasing operational overhead. The certificate authority market’s growth from $173.1 million in 2023 to a projected $401.4 million by 2030 reflects the rapidly growing demand for digital certificates. As certificate volumes surge, manual processes cannot scale, especially with shorter validity periods.
The Complete Timeline: From 398 to 47 Days
Table 1: Certificate Validity Reduction Timeline
| Phase |
Effective Date |
Maximum Validity |
Annual Renewals (per 1,000 certs) |
Daily Operations |
Key Changes |
| Current |
Present |
398 days |
917 |
2.5 |
Baseline |
| Phase 1 |
March 15, 2026 |
200 days |
1,825 |
5 |
First major reduction |
| Phase 2 |
March 15, 2027 |
100 days |
3,650 |
10 |
Acceleration phase |
| Phase 3 |
March 15, 2029 |
47 days |
7,766 |
21.3 |
Final implementation |
Source: CA/Browser Forum Ballot SC-081v3

Phase-by-Phase Breakdown
Phase 1: March 15, 2026 – The 200-Day Transition
The first reduction to 200 days (180 days plus a 20-day renewal window) represents a 50% decrease from the current validity. Organizations will experience:
- Doubling of renewal frequency from annual to semi-annual
- Initial stress testing of automation capabilities
- Identification of process bottlenecks
- First wave of forced modernization for legacy systems
The phased reduction aims to make the proposed changes “reasonable and attainable”, giving organizations time to adapt their infrastructure and processes. According to Gartner’s 2024 research on PKI challenges, PKI has become a bigger challenge for organizations than multi-factor authentication, with certificate lifecycle management complexity cited as a primary concern.
Phase 2: March 15, 2027 – The 100-Day Acceleration
The 100-day validity period marks the acceleration phase, where manual management begins breaking down:
- Certificates require renewal every three months
- Organizations face 10 daily operations for 1,000 certificates
- Manual tracking in spreadsheets becomes error-prone
- This phase triggers widespread automation adoption as organizations recognize that manual processes cannot scale
Learn more about essential automation protocols like ACME that enable this transition.
Phase 3: March 15, 2029 – The 47-Day Reality
The final 47-day maximum represents the end state where:
- Certificates expire every 6-7 weeks
- 21 daily renewal operations become the norm
- Domain revalidation occurs weekly
- Manual management becomes mathematically impossible
- Only automated systems can maintain compliance

Why Is the Industry Making This Change
Security Benefits of Shorter Lifespans
The CA/Browser Forum’s rationale for shorter certificates centers on three critical security improvements:
- Reduced exposure window: Compromised certificates remain valid for shorter periods
- Faster algorithm transitions: Deprecated cryptography phases out quickly
- Improved validation accuracy: Domain ownership verified more frequently
Shorter certificate lifecycles represent a fundamental shift in how the industry approaches digital trust and security resilience.
Addressing Modern Threat Vectors
Contemporary cybersecurity challenges demand shorter certificate lifecycles:
- Supply chain attacks: Compromised certificates in third-party integrations
- Insider threats: Reduced window for malicious certificate usage
- Cryptographic vulnerabilities: Faster response to algorithm weaknesses
- Compliance requirements: Meeting evolving regulatory standards like NIST, PCI, DORA etc
NIST emphasizes shorter validity periods as essential for maintaining security in rapidly evolving threat landscapes, particularly as organizations prepare for the post-quantum cryptography transition.
Browser Vendor Perspectives
Browser vendors unanimously support the change, viewing it as essential infrastructure modernization:
- Google Chrome (73% desktop browser market share) states that it provides enhanced protection through frequent validation, reduces the window of vulnerability for 3+ billion users
- Apple Safari believes it will improve ecosystem security across iOS, iPadOS, and macOS devices
- Mozilla Firefox thinks it brings alignment with modern web security standards and open web principles
- Microsoft Edge states it reduces the attack surface for enterprise environments and cloud services
The official voting record shows 29 votes in favor, zero opposed, unprecedented consensus in CA/Browser Forum history, demonstrating industry-wide commitment to this security evolution.
Impact Analysis: What This Means for Organizations
Timeline Compression Impact
When certificate validity drops to 47 days, organizations managing 1,000 certificates will execute 7,766 renewal operations annually. That’s 21 operations every single working day (calculated from CA/Browser Forum Ballot SC-081v3 requirements).
Federal agencies alone face a $7.1 billion migration cost to post-quantum cryptography by 2035, per White House Office of Management and Budget estimates, with NIST’s timeline mandating deprecation of RSA and ECDSA by 2030.
Organizations implementing automation achieve dramatic time savings, ranging from hours to minutes, in certificate management time, and completely eliminate certificate-related outages, resulting in millions of dollars in saved costs and protected revenue.
Explore our comprehensive guide on choosing the right certificate lifecycle management solution.
Table 2: Certificate Lifecycle Evolution – Manual vs. Automated Operations – 1000 certificates portfolio
| Metric |
Current State (398 days) |
2026 (200 days) |
2027 (100 days) |
2029 (47 days) |
With Automation |
| Annual Renewals (1,000 certs) |
917 |
1,825 |
3,650 |
7,766 |
7,766 (automated) |
| Daily Operations Required |
2.5 |
5 |
10 |
21.3 |
21.3 (automated) |
| FTE Hours Required Annually* |
2,751 (minimum) |
5,475 (minimum) |
10,950 (minimum) |
23,298 (minimum) |
500-750** |
| Average Time per Renewal |
3-4 hours |
3-4 hours |
3-4 hours |
3-4 hours |
<5 minutes*** |
| Compliance Audit Prep Time**** |
3-5 days |
5-7 days |
7-10 days |
10-15 days |
2-4 hours |
| Deployment Method |
Manual |
Manual |
Manual |
Manual |
API/Automated |
Source: Calculations based on CA/Browser Forum Ballot SC-081v3 timeline, assuming 3 hours average manual processing time per certificate and industry standard error rates from IETF RFC 8555
*Assumes standard renewals without complications. Complex deployments, failed validations, or emergency revocations require additional time and attention.
**The automation estimate includes monitoring, exception handling, and periodic system maintenance. Actual hours depend on automation maturity and infrastructure complexity
***ACME protocol challenges complete in under 15 seconds, with total renewal typically under 30 seconds including network latency. <5 minutes is a safe estimate.
****Audit preparation times are industry estimates and vary by organization size and compliance requirements.

Operational Impact by Organization Size
Table 3: 47-Day Certificate Impact by Organization Size
| Organization Size |
Certificate Count |
Daily Operations at 47 Days |
Annual FTE Hours* |
Automation Requirement |
| Small Business |
10-50 |
0.2-1 |
233-1,165 |
Recommended |
| Mid-Market |
100-500 |
2-11 |
2,330-11,649 |
Essential |
| Enterprise |
1,000-5,000 |
21-106 |
23,298-116,490 |
Critical |
| Global Enterprise |
10,000+ |
213+ |
232,980+ |
Mandatory |
*Based on industry estimates of 3 hours per manual certificate renewal and installation

Transforming Certificate Management into Competitive Advantage
Strategic Benefits of Early Adoption
Organizations that implement certificate lifecycle automation now transform this mandate from a compliance burden into a strategic enabler:
Operational Excellence:
- Eliminate manual renewal bottlenecks
- Reduce human error and misconfigurations
- Enable self-service certificate requests for development teams
- Free security teams to focus on strategic initiatives
Business Agility:
- Accelerate application deployment cycles
- Support rapid scaling for new services
- Enable seamless multi-cloud operations
- Reduce time-to-market for digital initiatives
Security Posture:
- Achieve complete certificate visibility across environments
- Enforce consistent security policies
- Enable rapid response to vulnerabilities
- Build a foundation for crypto-agility
Competitive Positioning:
- Demonstrate security maturity to customers and partners
- Meet stringent compliance requirements effortlessly
- Support modern DevOps and cloud-native architectures
- Position for future cryptographic transitions
Read about the seven stages of certificate management to understand the full lifecycle.
The Window of Opportunity
Organizations fall into three categories based on their preparation timeline:
Early Adopters (2024-2026):
- Smooth transition through all phases
- Time to refine processes and build expertise
- Competitive cost advantages through gradual implementation
- Enhanced security posture as a differentiator
- Complete preparation for the 2029 deadline
Pragmatic Majority (2026-2027):
- Adequate preparation time for Phases 1 and 2
- More compressed timeline for final transition
- Standard implementation approach
- Achievable but requires focus and resources
Late Adopters (2028-2029):
- Crisis-mode implementation
- Higher costs due to rushed deployment
- Limited optimization opportunities
- Operational disruption during transition
- Competitive disadvantage
The choice of timing directly impacts not only implementation success but also long-term operational efficiency and strategic positioning.
Take Action Now: Schedule a personalized demo to see how AppViewX can prepare your organization for the 47-day transition before Phase 1 begins in March 2026.
Future-Proofing Your Certificate Infrastructure
Prepare for Accelerating Change
- By 2030, quantum-vulnerable algorithms like RSA and ECDSA will be deprecated, and by 2035, they’ll be entirely disallowed per NIST’s post-quantum timeline
- Certificate validation data reuse periods continue shrinking
- New compliance requirements emerge regularly, including DORA and updated PCI DSS standards
Build Organizational Capabilities
- Develop internal expertise in certificate lifecycle management
- Establish partnerships with certificate automation providers
- Create documentation and training programs
- Assign clear responsibility for certificate management across teams
Measure and Optimize
Track key metrics:
- Mean time to certificate deployment
- Certificate-related incident frequency
- Compliance audit performance
- Automation coverage percentage
Learn about 10 best practices for continuous compliance when managing digital certificates.
Essential Capabilities for 47-Day Success
Effective automation platforms must provide comprehensive capabilities to handle the 47-day lifecycle. According to Gartner’s 2025 Buyers’ Guide for PKI and Certificate Lifecycle Management, organizations should prioritize:
- Automated discovery to maintain certificate visibility across hybrid and multi-cloud environments
- ACME protocol support for automated certificate issuance and renewal
- Policy enforcement to ensure compliance with organizational security standards
- Integration capabilities with existing infrastructure, CAs, and DevOps tools
- Monitoring and alerting for exception handling and proactive management
- Self-service workflows enabling developers while maintaining security controls
AVX ONE CLM provides these capabilities through a unified platform approach, enabling organizations to scale certificate operations without proportionally scaling team size. Recognized by Gartner’s for effectively managing organization’s certificates, AppViewX delivers enterprise-grade automation with proven results.
Building Crypto-Agility for the Future
Preparing for Post-Quantum Cryptography
The 47-day mandate prepares organizations for larger cryptographic transitions ahead:
NIST’s post-quantum cryptography timeline targets widespread adoption by 2035, requiring organizations to:
- Replace current cryptographic algorithms with quantum-resistant alternatives
- Support hybrid certificate approaches during transition periods
- Maintain backward compatibility while enhancing security
- Manage algorithm agility across diverse systems
Organizations with mature certificate automation can:
- Transition algorithms in weeks versus years for manual processes
- Test new cryptographic approaches without production risk
- Roll back quickly if issues emerge
- Maintain complete visibility during transitions
AppViewX PKI-as-a-Service positions organizations for post-quantum readiness while addressing today’s 47-day certificate requirements.
The Path to Crypto-Agility
Near-term (2025-2029):
- Master 47-day certificate lifecycle automation
- Build organizational muscle for rapid certificate operations
- Establish discovery and inventory practices
- Develop policy frameworks for cryptographic standards
Mid-term (2030-2033):
- Begin post-quantum cryptography testing
- Implement hybrid certificate support
- Update systems for algorithm agility
- Train teams on new cryptographic standards
Long-term (2034-2035+):
- Complete post-quantum transition
- Maintain crypto-agility for future algorithms
- Continuous cryptographic risk assessment
- Proactive adoption of emerging standards
Organizations that view 47-day certificates as an isolated compliance requirement miss the larger strategic opportunity. Those that build true crypto-agility gain a lasting competitive advantage.
Explore what the table stakes are for certificate lifecycle management in 2026 and beyond.
Take Your Next Step Toward 47-Day Certificate Readiness.
The transition to 47-day certificates is inevitable. The question isn’t whether to automate, but when and how. Organizations that act now will lead their industries in security posture, operational efficiency, and crypto-agility.
Choose Your Path Forward:
Schedule a Live Demo → See AppViewX in action with a personalized demonstration tailored to your environment
Download the Gartner Buyers’ Guide → Get expert guidance on evaluating PKI and CLM solutions
Contact Our Team → Discuss your specific requirements with our PKI experts
Uncategorized
Key Takeaways
- Automation reduces certificate management time by 73-82%, transforming 23,298 annual hours to just 500-750 hours for 1,000 certificates.
- Organizations face an average of 4 certificate-related outages over 2 years, with each incident costing $11.1 million per outage event
- ACME protocol enables automated certificate renewal with validation typically completed in seconds, compared to hours or days for manual processes
- Organizations typically discover 5-10 times more certificates than expected during automated discovery processes
- Implementation requires three phases: Discovery (2-4 weeks), Automation Deployment (6-8 weeks), and Enterprise Scale (3-6 months)
As TLS certificate validity periods compress from 398 days today to just 47 days by 2029, manual certificate management becomes increasingly challenging, ultimately transforming into a mathematically impossible task. Organizations managing a 1,000-certificate portfolio will require 21 certificate operations daily, excluding weekends and holidays. This technical guide provides a comprehensive blueprint for implementing certificate lifecycle automation, delivering measurable ROI while preparing your infrastructure for the future of digital identity management.
Understanding Certificate Lifecycle Automation
What Is Certificate Lifecycle Automation?
Certificate lifecycle automation encompasses the end-to-end orchestration of TLS certificate operations through programmatic workflows, eliminating the need for manual intervention. Unlike traditional approaches requiring human operators to track expiration dates, generate certificate signing requests (CSRs), and install certificates, automated systems handle the entire lifecycle, from initial provisioning through renewal and eventual decommissioning, without human touchpoints for standard operations.
Modern certificate lifecycle automation platforms such as AVX ONE integrate directly with certificate authorities (CAs), infrastructure components, and security tools to create a self-healing ecosystem. When a certificate approaches expiration, the system automatically initiates renewal, validates domain control, obtains the new certificate, deploys it across all endpoints, and verifies successful installation, all while maintaining comprehensive audit trails.
The Business Case for Automation
The certificate authority market’s growth from $173.1 million in 2023 to a projected $401.4 million by 2030 reflects the rapidly increasing demand for digital certificates. As certificate volumes surge, manual processes cannot scale. With 71% of IT professionals admitting they don’t know their actual certificate count, automation becomes essential for maintaining visibility and control.
The economic argument for certificate lifecycle automation extends beyond preventing outages. ITIC found that over 90% of respondents estimated their cost of downtime to be over $300,000 per hour, standing true even for small and midsize organizations upto 200 employees.

ITIC states that if you’re a micro SMB with less than 25 employees and one server, your downtime might be an “extremely conservative” $1,670 per minute or about $100,000 an hour.
Core Components of Automated PKI Management
Discovery and Inventory Management
Comprehensive discovery forms the foundation of successful automation. By utilising discovery tools, organisations typically uncover more certificates than are tracked in spreadsheets. The visibility gap creates significant risk, as unmanaged certificates become potential failure points.
Automated discovery must encompass:
- Network scanning for TLS endpoints
- Cloud service integration (AWS, Azure, Google Cloud)
- Container and Kubernetes pod inspection
- Load balancer and CDN certificate identification
- IoT device certificate cataloging
Automated discovery and up-to-date inventory are prerequisites for reaching upper maturity levels (4 & 5) as emphasized by The PKI Consortium’s maturity model for modern certificate management.
Automated Renewal and Provisioning
The ACME protocol (RFC 8555) revolutionizes certificate provisioning by enabling automated validation that typically completes in a matter of seconds. This represents a dramatic reduction from the manual process, which can take hours to days per certificate or even 10 days to a month for complete renewal and installation.
Policy Engine and Governance
Effective automation requires robust policy enforcement. AppViewX’s policy engine enables organisations to define and enforce standards for:
- Key specifications: Minimum key lengths (2048-bit RSA, 256-bit ECC)
- Certificate attributes: SAN requirements, validity periods, signature algorithms
- Approval workflows: Risk-based routing for high-value certificates
- Compliance requirements: Industry standards (PCI DSS, HIPAA, SOC 2)
As cryptographic standards evolve, automation must also support crypto-agility. According to NIST and NSA guidance, organizations should begin preparing for post-quantum cryptography transitions before 2030, making policy-driven automation a critical capability.
Implementation Blueprint: Three-Phase Approach

Phase 1: Discovery and Assessment
Begin with comprehensive visibility using automated certificate discovery tools to identify all certificates across your infrastructure. The Enterprise Strategy Group research shows non-human identities outnumber human ones by 20:1, making thorough discovery essential.
Key activities:
- Deploy agentless scanning across network segments
- Integrate with cloud platforms and container orchestrators
- Document certificate ownership and dependencies
- Calculate baseline metrics for ROI measurement
- Identify high-risk certificates for priority automation
Phase 2: Transform Core Processes Through Smart Automation
Automate Critical Workflows
Replace manual renewal checks with automated workflows. With platforms like AppViewX AVX ONE, certificates renew automatically before expiration without human intervention for standard requests. As CA/Browser Forum Baseline Requirements evolve, automation ensures continuous compliance across the organization.
Implement Policy-Driven Management
- Instant policy-driven revocation with complete audit trails
- Dynamic compliance dashboards replacing manual data collection]
- Automated compliance reporting, reducing quarterly audit preparation from days to hours
Establish Governance Frameworks
Form a cross-functional Machine Identity Management Working Group to:
Phase 3: Achieve Enterprise-Scale Automation and Crypto-Agility
Native Platform Integration
Replace custom scripts with native Kubernetes integration, enabling certificate delivery at DevOps speed. Certificates are provisioned automatically into containerised applications without blocking deployment pipelines. Learn here how to streamline certificate management in Azure Kubernetes Service for cloud-native environments.
Enterprise System Orchestration
Integrate certificate lifecycle management with:
Build Crypto-Agility for the Future
The White House National Security Memorandum 10 (NSM-10) mandates that federal agencies complete their migration to post-quantum cryptography by 2035. When post-quantum algorithms require deployment, automated systems must identify affected certificates, generate replacements, and deploy across environments in hours rather than months. Review NIST’s crypto-agility strategies to prepare your organization for this transition.
TLS Certificate Management Software Comparison
When evaluating certificate lifecycle automation platforms, consider these critical capabilities:
Essential Features
- Multi-CA support: Support for multiple certificate authorities to avoid vendor lock-in
- Protocol flexibility: ACME, SCEP, EST, and proprietary APIs
- Cloud-native architecture: Scalability for millions of certificates
- Zero-touch renewal: Fully automated renewal without human intervention
- Comprehensive discovery: Agentless scanning across hybrid infrastructure
Integration Requirements
Modern certificate lifecycle automation must integrate seamlessly with your existing technology stack. AppViewX’s integration ecosystem includes:
- ITSM platforms: ServiceNow, BMC Remedy, Jira Service Management
- Cloud providers: AWS Certificate Manager, Azure Key Vault, Google Certificate Authority Service
- DevOps tools: Jenkins, GitLab, Terraform, Ansible
- Security platforms: Splunk, QRadar, CyberArk
According to Gartner’s latest research, organizations prioritizing integration capabilities achieve 50% faster implementation and 30% lower total cost of ownership.
Measuring Success: KPIs and Metrics
Operational Metrics
Track these key performance indicators to demonstrate automation value:
- Mean Time to Provision (MTTP): Target <5 minutes from request to deployment
- Certificate coverage: Aim for 95%+ automated management
- Renewal success rate: Should exceed 99.9% with proper automation
- Discovery accuracy: Track percentage of certificates under management
- Policy compliance: Monitor adherence to security standards
Business Impact Metrics
Quantify automation ROI through:
- Outage prevention: Number of potential outages avoided
- Cost avoidance: Calculate savings from prevented incidents
- Productivity gains: FTE hours redirected to strategic initiatives
- Audit performance: Reduction in compliance preparation time
- Security posture: Decrease in certificate-related vulnerabilities
Preparing for Future Requirements
Post-Quantum Readiness
The White House National Security Memorandum 10 mandates federal agencies complete migration to post-quantum cryptography by 2035, with an estimated cost of $7.1 billion. Organisations implementing automation now position themselves for seamless algorithm transitions when NIST’s post-quantum standards become mandatory.
Automation enables crypto-agility through:
- Centralized algorithm management
- Rapid certificate replacement capabilities
- Hybrid certificate support during transition
- Automated vulnerability scanning and remediation
Container and Kubernetes Automation
According to Red Hat’s 2024 State of Kubernetes Security report, a majority of organizations experienced at least one container or Kubernetes security incident in the last 12 months, with 45% reporting runtime incidents and 44% encountering issues in build and deployment phases. As teams scale their cloud-native environments, these numbers highlight the importance of eliminating manual, error-prone steps, including certificate provisioning and renewal.
This is where automated certificate management becomes critical. AppViewX streamlines this by providing native integration for:
- Ingress controller certificate management
- Service mesh TLS automation
- Pod-to-pod encryption
- Secrets rotation and management
Best Practices for Implementation Success
Start Small, Scale Fast
- Begin with high-risk certificates where automation delivers immediate value
- Pilot with 20-30% of portfolio to build confidence and refine processes
- Document lessons learned and adjust automation policies
- Scale to production once pilot demonstrates success
- Achieve full coverage within 6-12 months
Avoid Common Pitfalls
Organizations often struggle with:
- Incomplete discovery leading to shadow IT certificates
- Over-complex approval workflows that negate automation benefits
- Insufficient testing causing production failures
- Lack of executive sponsorship delaying implementation
- Treating automation as purely technical rather than business transformation
Build Organizational Capability
Successful automation requires cultural change:
- Train teams on automation tools and processes
- Establish clear ownership and accountability
- Create cross-functional working groups
- Document procedures and runbooks
- Celebrate automation wins to build momentum
The Path Forward: Taking Action
The transition to 47-day certificates isn’t a future consideration—it’s an immediate imperative. Organizations implementing certificate lifecycle automation now gain competitive advantages through operational efficiency, enhanced security, and infrastructure resilience.
Immediate Next Steps
- Assess your current state using the PKI Consortium’s maturity model
- Calculate your ROI potential based on certificate volume and outage history
- Evaluate automation platforms against your specific requirements
- Start discovery to understand your true certificate footprintBuild your business case with concrete metrics and timelines
- Build your business case with concrete metrics and timelines
Why AppViewX for Certificate Lifecycle Automation
AppViewX’s certificate lifecycle automation platform delivers:
- Comprehensive discovery across hybrid multi-cloud environments
- Policy-driven automation with zero-touch renewal
- Enterprise integrations with existing security and IT tools
- Crypto-agility for post-quantum readiness
- Proven ROI with customers achieving 70-90% reduction in management overhead across certificate lifecycle operations
Ready to transform your certificate management? Schedule a demo to see how AppViewX can automate your certificate lifecycle, or download our ROI calculator to quantify your automation opportunity
About AppViewX
AppViewX is a global leader in certificate lifecycle automation and machine identity management. Our platform enables enterprises to discover, manage, and automate certificates at scale across complex hybrid multi-cloud environments. With AppViewX, organizations achieve operational excellence while building crypto-agility for future security requirements.
Schedule Your Demo →
Uncategorized
Summary:
Use a Public CA when you need certificates for public-facing websites, customer applications, or any service accessed by external users, as public CAs are automatically trusted by all browsers and devices. Use a Private CA when securing internal networks, development environments, IoT devices, or any infrastructure where certificates only need to be trusted within your organization. Most enterprises need both: public CAs for external-facing services and private CAs for internal infrastructure, best managed through a unified certificate lifecycle management platform.
Consider weaving in CA-agnostic capabilities in the setup and conclusion as AppViewX is CA agnostic eliminating the threat of vendor locking.
Key Differences:
| Aspect |
Public CA |
Private CA |
| Best For |
Public websites, customer-facing apps, external APIs |
Internal networks, DevOps, IoT, employee authentication |
| Trust |
Automatic browser/device trust |
Manual trust deployment required |
| Cost Model |
Pay per certificate |
Setup cost + unlimited issuance |
| Certificate Transparency |
Required (public logs) |
Not required (privacy maintained) |
| Ideal Volume |
Low to medium volumes |
High volume needs (1000+ certificates) |
| Control |
Limited customization |
Full policy control |

Understanding Certificate Authorities (CAs): The Foundation of PKI
What is a Public Certificate Authority?
A Public Certificate Authority (CA) is a trusted third-party organization that issues SSL/TLS certificates for websites and applications accessible on the public internet. Public CAs are recognized and trusted by all major browsers and operating systems.
When you purchase an TLS certificate for your public-facing website, you’re obtaining it from a public CA that has been vetted and included in browser trust stores. These certificates enable the HTTPS connections users see when visiting secure websites.
What is a Private Certificate Authority?
Organizations often need to secure their internal infrastructure, applications, and users with digital certificates. When an organization establishes the capability to issue these certificates internally, it becomes a Private Certificate Authority. Private CA creates certificates that are only trusted within the organization’s own environment.
Which type of CA is right for your organization
The decision between Private CA and Public CA isn’t about choosing the “best” solution, it’s about matching your certificate infrastructure to your organization’s specific needs, scale, and growth trajectory. With the PKI market projected to reach USD 24.37 billion by 2032, growing at 20.1% annually, and Cloud/Managed PKI solutions expanding at 21.3% CAGR, you’re making this decision in a landscape where automation and scalability are no longer optional, they’re business necessities and competitive advantages.

Your path forward starts with understanding where certificates fit in your architecture today and where they need to take you tomorrow. Organizations currently manage thousands of internal certificates, yet still rely on spreadsheets for tracking. If that sounds familiar, you’re not behind, you’re at the perfect inflection point to build a certificate strategy that scales with your business rather than against it.
Public CA makes sense when you need immediate, universal trust. If your certificates protect customer-facing websites, e-commerce platforms, or services that external parties must validate, Public CA ensures trust through pre-installed root certificates in browsers and operating systems.
Private CA unlocks flexibility and scale for internal operations. When you’re securing internal applications, service-to-service communication, VPN access, or IoT device authentication, Private CA lets you define your own certificate policies, validity periods, and issuance workflows.
Automation for Public and Private CAs
The shift to automated certificate lifecycle management isn’t just about keeping pace with industry changes, it’s about positioning your organization to move faster and maintain digital trust. With recent CA/Browser Forum changes and a timeline that leads to 47-day certificate validity by March 2029 and machine identities growing 20 times faster than human identities, the organizations that automate today gain operational agility that compounds over time.
AVX ONE accelerates your automation journey. AppViewX helps companies manage their Certificate Authorities (CAs) by providing powerful certificate lifecycle management (CLM) solutions that automate, unify, and secure certificate operations across both public and private CAs in hybrid and multi-cloud environments. Rather than building custom integrations or managing multiple point solutions, it provides enterprise-grade certificate lifecycle automation that delivers results from day one.
The platform discovers certificates across your entire infrastructure regardless of issuer, automates end-to-end workflows from CSR (Certificate Signing Request) generation through deployment, and provides unified visibility across hybrid and multi-cloud environments.
Schedule Your Demo →